Kaspersky Lab Automatic Exploit Prevention technology, embedded in most of the company’s endpoint solutions, has detected a series of targeted cyber-attacks. The attacks were attempted by a new piece of malware that exploited a previously unknown zero-day vulnerability in the Microsoft Windows operating system. The intension was for cybercriminals to gain persistent access to victim systems in the Middle East. The vulnerability was patched by Microsoft on 9 October.
An attak via a zero-day vulnerability is one of the most dangerous forms of cyberthreat, as it involves the exploitation of a vulnerability that is yet to be discovered and fixed. If found by threat actors, a zero-day vulnerability can be used for the creation of an exploit that will open access to a whole system. This attack scenario is widely used by sophisticated actors in APT attacks, and was used here.
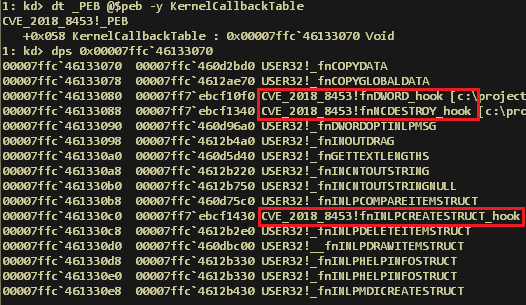
The discovered Microsoft Windows exploit was delivered to the victims via a PowerShell backdoor. It was then executed in order to get the necessary privileges for persistence on victim systems. The code of the malware was of high quality and was written to enable the reliable exploitation of as many different Windows builds as possible.
The cyber-attacks targeted less than a dozen of various organisations in the Middle East during the late summer. It is suspected that the actor behind the attack could be related to the FruityArmor group – as a PowerShell backdoor has exclusively been used by this threat actor in the past. Upon discovery, Kaspersky Lab’s experts immediately reported the vulnerability to Microsoft.
Kaspersky Lab products detected this exploit proactively through the following technologies:
- Via Kaspersky Lab’s behavioral detection engine, and Automatic Exploit Prevention components inside the company’s security products
- Through Advanced Sandboxing and the Antimalware engine within the Kaspersky Anti Targeted Attack Platform
“When it comes to zero-day vulnerabilities, it is critical to actively monitor the threat landscape on for new exploits. At Kaspersky Lab, our constant threat intelligence research aims to not only find new attacks, and establish the targets of different cyberthreat actors, we are also intent at learning what malicious technologies these criminals use. As a result of our research, we have a foundation layer of detection technologies which let us prevent attacks – such as the one that intended to use this vulnerability,” said Anton Ivanov, security expert at Kaspersky Lab.
To avoid zero-day exploits Kaspersky Lab recommends implementing the following technical measures:
- Avoid using software that is known to be vulnerable or recently used in cyber-attacks.
- Make sure that the software used in your company is regularly updated to the most recent versions. Security products with Vulnerability Assessment and Patch Management capabilities may help to automate these processes.
- Use a robust security solution such as Kaspersky Endpoint Security for Business that is equipped with behaviour-based detection capabilities for effective protection against known and unknown threats including exploits.
Find more details on Securelist.com.